A. Explain the purpose of the switch’s forwarding database.
Both bridges and switches build a forwarding database. The database is a list of Data Link (MAC) addresses and the port used to reach the device. Bridges and switches can automatically learn about devices to build the forwarding database. A network administrator can also program the device database manually. Bridges and switches use the following process to dynamically build the forwarding database:
- The process begins by examining the source address of an incoming packet. If the source address is not in the forwarding database, an entry for the address is made in the database. The port it came in on is also recorded.
- The destination address is then examined.
- If the destination address is in the database, the packet is forwarded to the appropriate port if the port is different than the one on which it was received.
- If the destination address is not in the database, the packet is sent out all ports except for the one on which it was received. This is known as flooding.
- A broadcast packet is forwarded (flooded) to all ports except the one on which it was received.
Transparent bridges forward packets only if the following conditions are met.
- The frame contains data from the layers above the Data Link layer.
- The frame’s integrity has been verified through a valid Cyclic Redundancy Check (CRC).
- The frame is not addressed to the bridge.
How switches forward packets depends on the switch type. The following table compares the different methods the switch uses to forward packets (some Cisco switches support all three methods).
- Store and forward: The switch buffers and verifies each frame before forwarding it.
- Cut through: The switch reads only up to the frame’s hardware address before starting to forward it. Cut-through switches have to fall back to store and forward if the outgoing port is busy at the time the packet arrives. There is no error checking with this method.
- Fragment free: A method that attempts to retain the benefits of both store and forward and cut through. Fragment free checks the first 64 bytes of the frame, where addressing information is stored. According to Ethernet specifications, collisions should be detected during the first 64 bytes of the frame, so frames that are in error because of a collision will not be forwarded. This way the frame will always reach its intended destination. Error checking of the actual data in the packet is left for the end device.
- Adaptive switching: A method of automatically selecting between the other three modes.
Note: Newer switches can monitor each port and determine which switching method to use. They can automatically change to store-and-forward if the number of errors on a port exceeds a configurable threshold.
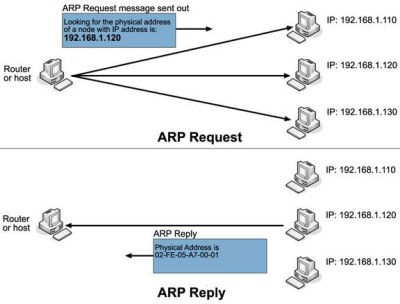
B. Explain the purpose and functionality of ARP
Address Resolution Protocol (ARP) is a telecommunications protocol used for resolution of network layer addresses into link layer addresses, a critical function in multiple-access networks. ARP is used to convert an IP address to a physical address such as an Ethernet address. ARP has been implemented with many combinations of network and data link layer technologies, such as IPv4, Chaosnet, DECnet and Xerox PARC Universal Packet (PUP) using IEEE 802 standards, FDDI, X.25, Frame Relay and Asynchronous Transfer Mode (ATM). IPv4 over IEEE 802.3 and IEEE 802.11 is the most common case. In Internet Protocol Version 6 (IPv6) networks, the functionality of ARP is provided by the Neighbor Discovery Protocol (NDP).
For example, the computers Matterhorn and Washington are in an office, connected to each other on the office local area network by Ethernet cables and network switches, with no intervening gateways or routers. Matterhorn wants to send a packet to Washington. Through other means, it determines that Washington’s IP address is 192.168.0.55. In order to send the message, it also needs to know Washington’s MAC address. First, Matterhorn uses a cached ARP table to look up 192.168.0.55 for any existing records of Washington’s MAC address (00:eb:24:b2:05:ac). If the MAC address is found, it sends the IP packet on the link layer to address 00:eb:24:b2:05:ac via the local network cabling. If the cache did not produce a result for 192.168.0.55, Matterhorn has to send a broadcast ARP message (destination FF:FF:FF:FF:FF:FF Mac address which is accepted by all computers) requesting an answer for 192.168.0.55. Washington responds with its MAC address (and its IP). Washington may insert an entry for Matterhorn into its own ARP table for future use. The response information is cached in Matterhorn’s ARP table and the message can now be sent.[1]
C. Explain the purpose and functionality of MAC addresses
A media access control address (MAC address) is a unique identifier assigned to network interfaces for communications on the physical network segment. MAC addresses are used as a network address for most IEEE 802 network technologies, including Ethernet. Logically, MAC addresses are used in the media access control protocol sublayer of the OSI reference model. The standard (IEEE 802) format for printing MAC-48 addresses in human-friendly form is six groups of two hexadecimal digits, separated by hyphens (-) or colons (:), in transmission order (e.g. 01-23-45-67-89-ab or 01:23:45:67:89:ab ). This form is also commonly used for EUI-64. Another convention used by networking equipment uses three groups of four hexadecimal digits separated by dots (.) (e.g. 0123.4567.89ab ), again in transmission order.
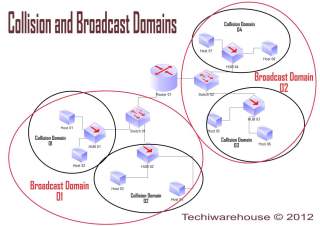
D. Explain the purpose and functionality of a broadcast domain.
A broadcast domain is a logical division of a computer network, in which all nodes can reach each other by broadcast at the data link layer. A broadcast domain can be within the same LAN segment or it can be bridged to other LAN segments.
In terms of current popular technologies: Any computer connected to the same Ethernet repeater or switch is a member of the same broadcast domain. Further, any computer connected to the same set of inter-connected switches/repeaters is a member of the same broadcast domain. Routers and other higher-layer devices form boundaries between broadcast domains.
This is as compared to a collision domain, which would be all nodes on the same set of inter-connected repeaters, divided by switches and learning bridges. Collision domains are generally smaller than, and contained within, broadcast domains.
While some layer two network devices are able to divide the collision domains, broadcast domains are only divided by layer 3 network devices such as routers or layer 3 switches. Separating VLANs divides broadcast domains as well, but provides no means to network these without layer 3 functionality.
The distinction between broadcast and collision domains comes about because simple Ethernet and similar systems use a shared transmission system. In simple Ethernet (without switches or bridges), data frames are transmitted to all other nodes on a network. Each receiving node checks the destination address of each frame, and simply ignores any frame not addressed to its own MAC.
Switches act as buffers, receiving and analyzing the frames from each connected network segment. Frames destined for nodes connected to the originating segment are not forwarded by the switch. Frames destined for a specific node on a different segment are sent only to that segment. Only broadcast frames are forwarded to all other segments. This reduces unnecessary traffic and collisions.
In such a switched network, transmitted frames may not be received by all other reachable nodes. Nominally, only broadcast frames will be received by all other nodes. Collisions are localized to the network segment they occur on. Thus, the broadcast domain is the entire inter-connected layer two network, and the segments connected to each switch/bridge port are each a collision domain.
E. Explain the purpose and functionality of VLANS
In computer networking, a single layer-2 network may be partitioned to create multiple distinct broadcast domains, which are mutually isolated so that packets can only pass between them via one or more routers; such a domain is referred to as a Virtual Local Area Network, Virtual LAN or VLAN.
Network architects set up VLANs to provide the segmentation services traditionally provided only by routers in LAN configurations. VLANs address issues such as scalability, security, and network management. Routers in VLAN topologies provide broadcast filtering, security, address summarization, and traffic-flow management. By definition, switches may not bridge IP traffic between VLANs as doing so would violate the integrity of the VLAN broadcast domain.
VLANs can also help create multiple layer 3 networks on the same layer 2 switch. For example, if a DHCP server is plugged into a switch it will serve any host on that switch that is configured to get its IP from a DHCP server. By using VLANs you can easily split the network up so some hosts won’t use that DHCP server and will obtain link-local addresses, or obtain an address from a different DHCP server. Hosts may also use a DNS server if a DHCP is not available.
VLANs are layer 2 constructs, compared with IP subnets, which are layer 3 constructs. In an environment employing VLANs, a one-to-one relationship often exists between VLANs and IP subnets, although it is possible to have multiple subnets on one VLAN. VLANs and IP subnets provide independent layer 2 and layer 3 constructs that map to one another and this correspondence is useful during the network design process.
By using VLANs, one can control traffic patterns and react quickly to relocations. VLANs provide the flexibility to adapt to changes in network requirements and allow for simplified administration.
Partitioning a local network into several distinctive segments for e.g.
- production
- Voice over IP
- network management
- storage area network (SAN)
- guest network
- demilitarized zone (DMZ)
in a common infrastructure shared across VLAN trunks can provide a very high level of security with great flexibility to a comparatively low cost. Quality of Service schemes can optimize traffic on trunk links for real time (VoIP) or low-latency requirements (SAN).
VLANs could also be used in a school or work environment to provide easier access to local networks, to allow for easy administration, and to prevent disruption on the network.
In cloud computing VLANs, IP addresses, and MAC addresses on them are resources which end users can manage. Placing cloud-based virtual machines on VLANs may be preferable to directly on the Internet to avoid security issues.
F. Explain the purpose and functionality of link aggregation
Link aggregation is a computer networking term to describe various methods of combining (aggregating) multiple network connections in parallel to increase throughput beyond what a single connection could sustain, and to provide redundancy in case one of the links fails.
In addition to the IEEE link aggregation substandards, there are a number of proprietary aggregation schemes including Cisco’s EtherChannel and Port Aggregation Protocol, AVAYA’s Multi-Link Trunking, Split Multi-Link Trunking, Routed Split Multi-Link Trunking and Distributed Split Multi-Link Trunking, ZTE’s “Smartgroup”, or Huawei’s “EtherTrunk”. Most high-end network devices support some kind of link aggregation, and software-based implementations – such as the *BSD lagg package, Linux’ bonding driver, Solaris’ dladm etc. – also exist for many operating systems.
===
[1] Chappell, Laura A. and Tittel, Ed. Guide to TCP/IP, Third Edition. Thomson Course Technology, 2007, pp. 115-116.
See more at:






Leave a comment