I started the study guide for the first part of this certification last year. You can check it out here. After some great feedback, I’ve decided to start the Study Guide for the second part of the certification, Implementing Cisco Cybersecurity Operations (SECOPS). I also was accepted on cohort 7 for the scholarship. The scholarship is still available at the time of this post, and it can be accessed here. I will try to follow the blueprint as close as possible, but I will leave some topics for later in the year after I learned a little more about them.
1.0 Endpoint Threat Analysis and Computer Forensics
1.1 Interpret the output report of a malware analysis tool such as AMP Threat Grid and Cuckoo Sandbox.
1.2 Describe these terms as they are defined in the Common Vulnerability Scoring System (CVSS 3.0):
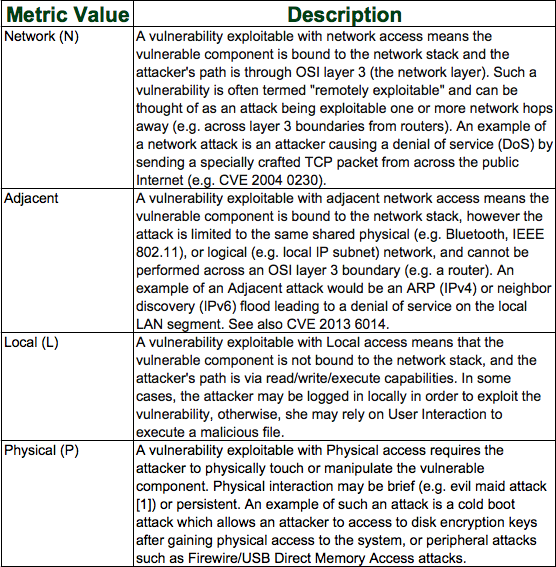
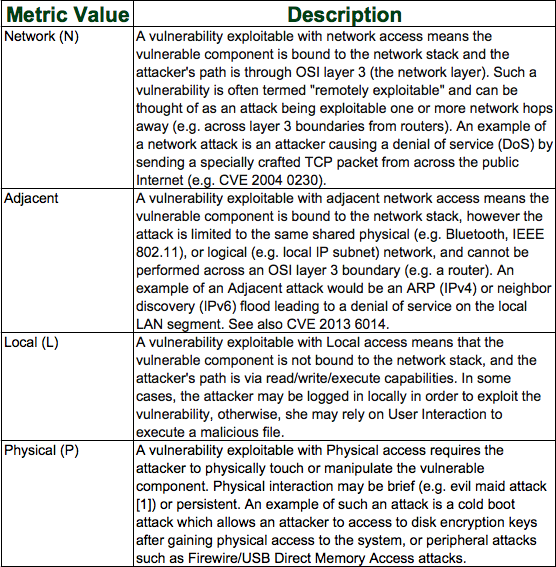
a. Attack Vector (AV): This metric reflects the context by which vulnerability exploitation is possible. This metric value (and consequently the Base score) will be larger the more remote (logically, and physically) an attacker can be in order to exploit the vulnerable component. The assumption is that the number of potential attackers for a vulnerability that could be exploited from across the Internet is larger than the number of potential attackers that could exploit a vulnerability requiring physical access to a device, and therefore warrants a greater score. The list of possible values is presented in Figure 1.
Figure 1: Attack Vector
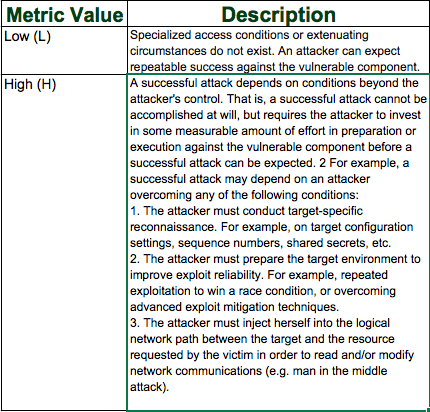
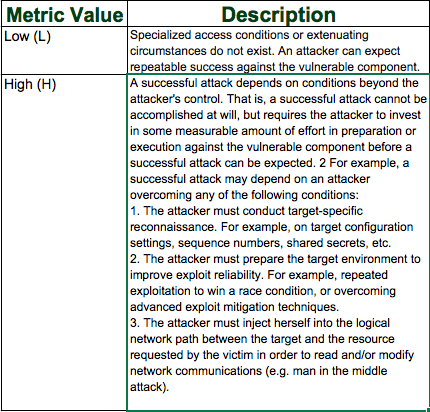
b. Attack Complexity (AC): This metric describes the conditions beyond the attacker’s control that must exist in order to exploit the vulnerability. As described below, such conditions may require the collection of more information about the target, the presence of certain system configuration settings, or computational exceptions. Importantly, the assessment of this metric excludes any requirements for user interaction in order to exploit the vulnerability (such conditions are captured in the User Interaction metric). This metric value is largest for the least complex attacks. The list of possible values is presented in Figure 2.
Figure 2: Attack Complexity
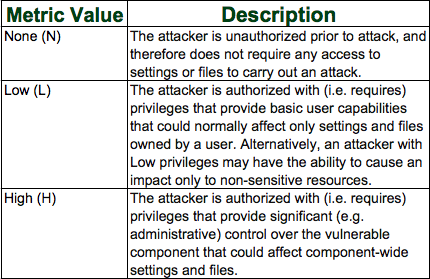
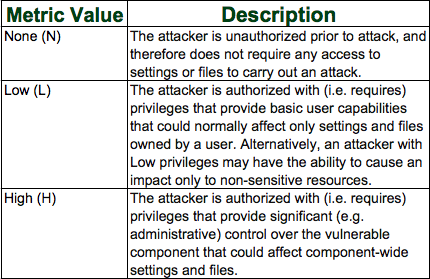
c. Privileges Required (PR): This metric describes the level of privileges an attacker must possess before successfully exploiting the vulnerability. This metric is greatest if no privileges are required. The list of possible values is presented in Figure 3.
Figure 3: Privileges Required
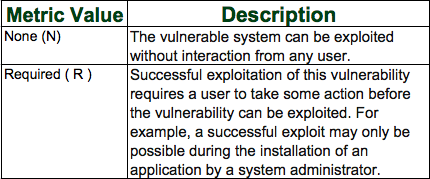
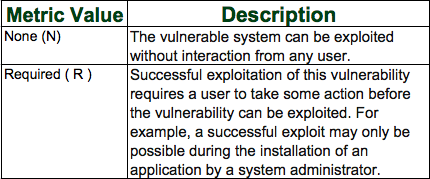
d. User interaction (UI): This metric captures the requirement for a user, other than the attacker, to participate in the successful compromise of the vulnerable component. This metric determines whether the vulnerability can be exploited solely at the will of the attacker, or whether a separate user (or user-initiated process) must participate in some manner. This metric value is greatest when no user interaction is required. The list of possible values is presented in Figure 4.
Figure 4: User Interaction
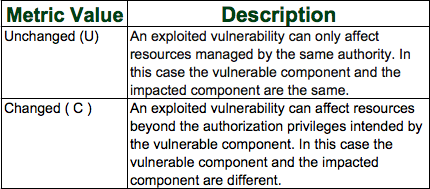
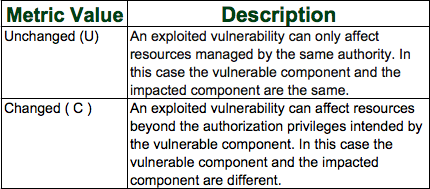
e. Scope (S): An important property captured by CVSS v3.0 is the ability for a vulnerability in one software component to impact resources beyond its means or privileges. This consequence is represented by the metric Authorization Scope, or simply Scope. Formally, Scope refers to the collection of privileges defined by a computing authority (e.g., an application, an operating system, or a sandbox environment) when granting access to computing resources (e.g., files, CPU, memory, etc.). These privileges are assigned based on some method of identification and authorization. In some cases, the authorization may be simple or loosely controlled based on predefined rules or standards. For example, in the case of Ethernet traffic sent to a network switch, the switch accepts traffic that arrives on its ports and is an authority that controls the traffic flow to other switch ports. When the vulnerability of a software component governed by one authorization scope can affect resources governed by another authorization scope, a Scope change has occurred. Intuitively, one may think of a scope change as breaking out of a sandbox, and an example would be a vulnerability in a virtual machine that enables an attacker to delete files on the host OS (perhaps even its own VM). In this example, there are two separate authorization authorities: one that defines and enforces privileges for the virtual machine and its users, and one that defines and enforces privileges for the host system within which the virtual machine runs. A scope change would not occur, for example, with a vulnerability in Microsoft Word that allows an attacker to compromise all system files of the host OS, because the same authority enforces privileges of the user’s instance of Word, and the host’s system files. The Base score is greater when a scope change has occurred. The list of possible values is presented in Figure 5.
Figure 5: Scope
1.3 Describe these terms as they are defined in the Common Vulnerability Scoring System (CVSS 3.0):
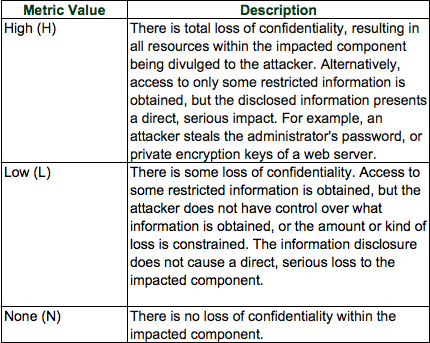
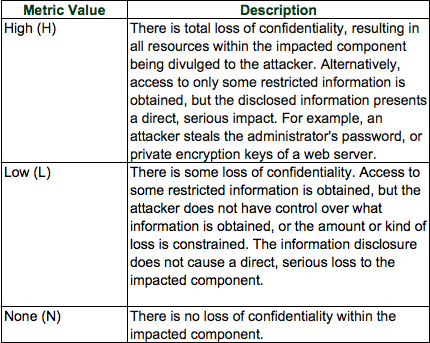
a. Confidentiality Impact (C): This metric measures the impact to the confidentiality of the information resources managed by a software component due to a successfully exploited vulnerability. Confidentiality refers to limiting information access and disclosure to only authorized users, as well as preventing access by, or disclosure to, unauthorized ones. The list of possible values is presented in Figure 6. This metric value increases with the degree of loss to the impacted component.
Figure 6: Confidentiality Impact
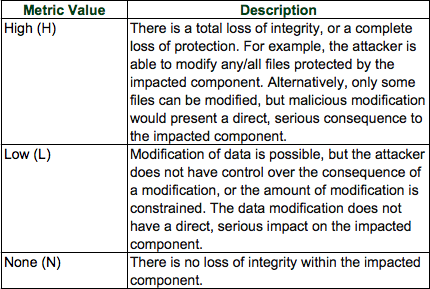
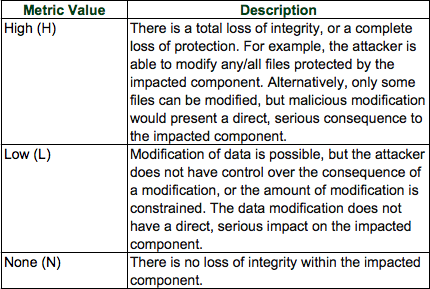
b. Integrity Impact (I): This metric measures the impact on the integrity of a successfully exploited vulnerability. Integrity refers to the trustworthiness and veracity of information. The list of possible values is presented in Figure 7. This metric value increases with the consequence to the impacted component.
Figure 7: Integrity Impact
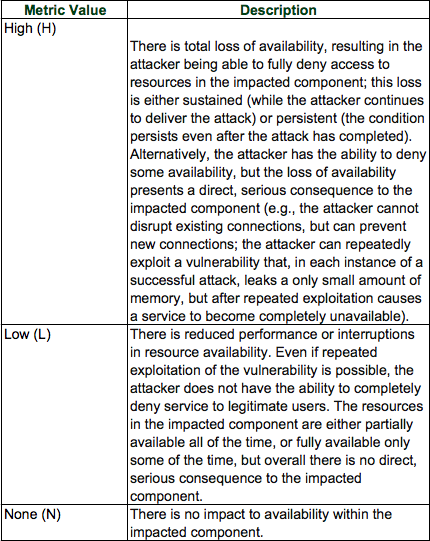
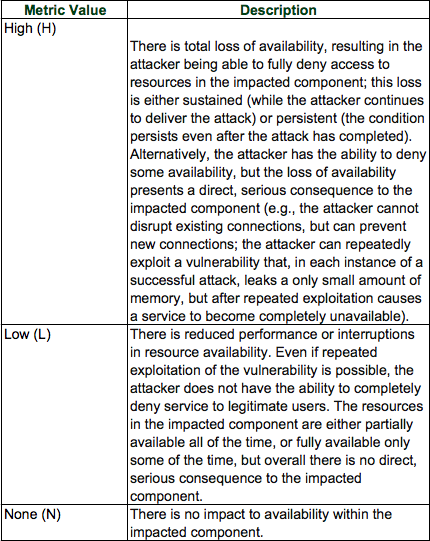
c. Availability Impact (A): This metric measures the impact to the availability of the impacted component resulting from a successfully exploited vulnerability. While the Confidentiality and Integrity impact metrics apply to the loss of confidentiality or integrity of data (e.g., information, files) used by the impacted component, this metric refers to the loss of availability of the impacted component itself, such as a networked service (e.g., web, database, email). Since availability refers to the accessibility of information resources, attacks that consume network bandwidth, processor cycles, or disk space all impact the availability of an impacted component. The list of possible values is presented in Figure 8. This metric value increases with the consequence to the impacted component.
Figure 8: Availability Impact
1.4 Define these items as they pertain to the Microsoft Windows file system
a. FAT32: is an updated version of the FAT (File Allocation Table) file system created in 1977 by Microsoft. It is a computer file system architecture and a family of industry-standard file systems utilizing it. With FAT32 you’re limited to 2TB FAT32 partitions and 4GB maximum size files.
b. NTFS (New Technology Files System): is a proprietary file system developed by Microsoft.
c. Alternative data streams:Alternate Data Streams (ADS) is a file attribute only found on the NTFS file system. You’ll need a tool like streams to view this data. Here is an example.
d. MACE: NTFS keeps track of lots of time stamps. Each file has a time stamp for ‘Create’, ‘Modify’, ‘Access’, and ‘Entry Modified’. The latter refers to the time when the MFT entry itself was modified. These four values are commonly abbreviated as the ‘MACE’ values. Note that other attributes in each MFT record may also contain timestamps that are of forensic value.
1. MFT (Master File Table): The NTFS file system contains a file called the master file table, or MFT. There is at least one entry in the MFT for every file on an NTFS file system volume, including the MFT itself. All information about a file, including its size, time and date stamps, permissions, and data content, is stored either in MFT entries, or in space outside the MFT that is described by MFT entries.
e. EFI: The EFI system partition (ESP) is a partition on a data storage device (usually a hard disk drive or solid-state drive) that is used by computers adhering to the Unified Extensible Firmware Interface (UEFI).
- 1. UEFI: The Unified Extensible Firmware Interface (UEFI) is a specification that defines a software interface between an operating system and platform firmware.
f. Free space: See File system, it refers to the unallocated space in a file system.
g. Timestamps on a file system: File properties in regards of date and time.
1.5 Define these terms as they pertain to the Linux file system
a. EXT4: The ext4 or fourth extended filesystem is a journaling file system for Linux, developed as the successor to ext3.
b. Journaling: A journaling file system is a file system that keeps track of changes not yet committed to the file system’s main part by recording the intentions of such changes in a data structure known as a “journal”, which is usually a circular log.
c. Master Boot Record (MBR): is a special type of boot sector at the very beginning of partitioned computer mass storage devices like fixed disks or removable drives intended for use with IBM PC-compatible systems and beyond. The MBR holds the information on how the logical partitions, containing file systems, are organized on that medium. The MBR also contains executable code to function as a loader for the installed operating system—usually by passing control over to the loader’s second stage, or in conjunction with each partition’s volume boot record (VBR). This MBR code is usually referred to as a boot loader.
d. Swap filesystem: Swap space in Linux is used when the amount of physical memory (RAM) is full. If the system needs more memory resources and the RAM is full, inactive pages in memory are moved to the swap space. While swap space can help machines with a small amount of RAM, it should not be considered a replacement for more RAM. Swap space is located on hard drives, which have a slower access time than physical memory.
e. MAC: In cryptography, a message authentication code (MAC), sometimes known as a tag, is a short piece of information used to authenticate a message—in other words, to confirm that the message came from the stated sender (its authenticity) and has not been changed. The MAC value protects both a message’s data integrity as well as its authenticity, by allowing verifiers (who also possess the secret key) to detect any changes to the message content.
1.6 Compare and contrast three types of evidence
a. Best evidence: Original, unaltered evidence. In court, this is preferred over secondary evidence.The best evidence rule is a legal principle that holds an original copy of a document as superior evidence.
b. Corroborative evidence: (or corroboration) is evidence that supports a proposition already supported by initial evidence, therefore confirming the original proposition.
c. Indirect Evidence (Circumstantial): Circumstantial evidence is evidence that relies on an inference to connect it to a conclusion of fact—like a fingerprint at the scene of a crime. By contrast, direct evidence supports the truth of an assertion directly—i.e., without need for any additional evidence or inference.
1.7 Compare and contrast two types of image (both refer to Integrity, see above)
a. Altered disk image: A system image with a compromised integrity.
b. Unaltered disk image: An image that has not been tampered with and that will provide the same result as the original when applied a hash algorithm like MD5.
1.8 Describe the role of attribution (“action of bestowing or assigning”) in an investigation. (Cyber attribution is the process of tracking, identifying and laying blame on the perpetrator of a cyberattack or other hacking exploit). This a nice read on the problem of attribution.
a. Assets: In information security, computer security and network security, an asset is any data, device, or other component of the environment that supports information-related activities.
b. Threat actor: Responsible for the cyberattack.
In future posts I will try to cover the following topics:
- Network Intrusion Analysis
- Incident Response
- Data and Event Analysis
- Incident Handling